While the concept of stealth addresses appears complex in theory, Buterin previously described it as a “low-tech approach” compared to other Ethereum privacy solutions. Ethereum co-founder Vitalik Buterin has shared a possible solution to what he describes as the “largest remaining challenge” on Ethereum — privacy. In a blog post on Jan. 20, Buterin acknowledged […]
While the concept of stealth addresses appears complex in theory, Buterin previously described it as a “low-tech approach” compared to other Ethereum privacy solutions.
Ethereum co-founder Vitalik Buterin has shared a possible solution to what he describes as the “largest remaining challenge” on Ethereum — privacy.
In a blog post on Jan. 20, Buterin acknowledged the need to come up with a privacy solution because by default, all information that goes onto a “public blockchain” is public too.
He then arrived at the concept of “stealth addresses” — which he said can potentially anonymize peer-to-peer transactions, nonfungible token (NFT) transfers, and Ethereum Name Service (ENS) registrations, protecting users.
An incomplete guide to stealth addresses:https://t.co/21Q18BrD30
— vitalik.eth (@VitalikButerin) January 20, 2023
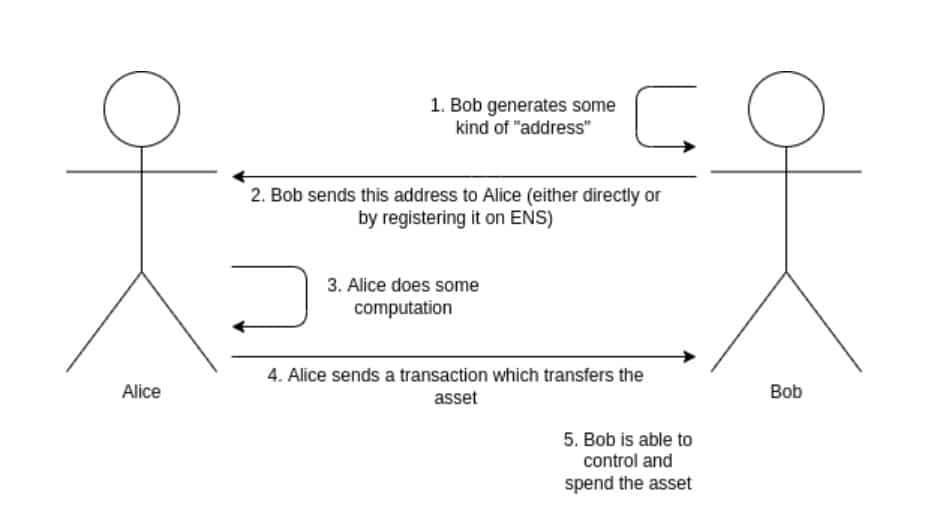
In the blog post, Buterin explained how on-chain transactions can be carried out between two parties with anonymity.
Firstly, a user looking to receive assets will generate and keep a “spending key” that is then used to generate a stealth meta-address.
This address — which can be registered on ENS — is then passed onto the sender who can perform a cryptographic computation on the meta-address to generate a stealth address, which belongs to the receiver.
The sender can then transfer assets to the receiver’s stealth address in addition to publishing a temporary key to confirm that the stealth address belongs to the receiver.
The effect of this is that a new stealth address is generated for each new transaction.
Buterin noted that a “Diffie-Hellman key exchange” in addition to a “key blinding mechanism” would need to be implemented to ensure that the link between the stealth address and the user’s meta-address can’ be seen publicly.
The Ethereum co-founder added that ZK-SNARKs — a cryptographic-proof technology with built-in privacy features — could transfer funds to pay transaction fees.
However Buterin emphasized that this may lead to problems of its own — at least for the short term — stating “this costs a lot of gas, an extra hundreds of thousands of gas just for a single transfer.”
Related: Crypto privacy is in greater jeopardy than ever before — here’s why
Stealth addresses have long been touted as a solution to address on-chain privacy issues, which have been worked on since as early as 2014. However very few solutions have been brought to market thus far.
It also isn’t the first time Buterin has discussed the concept of stealth addresses in Ethereum.
In August, he dubbed stealth addresses as a “low-tech approach” for anonymously transferring ownership of ERC-721 tokens — otherwise known as NFTs.
The Ethereum co-founder explained that the stealth address concept proposed offers privacy differently to that of the now U.S. Office of Foreign Asset Control (OFAC)-sanctioned Tornado Cash:
”Tornado Cash can hide transfers of mainstream fungible assets such as ETH or major ERC20s […] but it’s very weak at adding privacy to transfers of obscure ERC20s, and it cannot add privacy to NFT transfers at all.”
Buterin offered some advice to Web3 projects that are developing a solution:
“Basic stealth addresses can be implemented fairly quickly today, and could be a significant boost to practical user privacy on Ethereum.”
“They do require some work on the wallet side to support them. That said, it is my view that wallets should start moving toward a more natively multi-address model […] for other privacy-related reasons as well,” he added.
Buterin suggested that stealth addresses may introduce “longer-term usability concerns,” such as social recovery issues. However, he is confident the problems can be properly addressed in time:
“In the longer term, these problems can be solved, but the stealth address ecosystem of the long term is looking like one that would really heavily depend on zero-knowledge proofs,” he explained.